NIST-compliant Post-Quantum Cryptography software:
Introduction
Cybersecurity is entering a new era — and most businesses aren’t ready for it.
Quantum computing is no longer theoretical. Companies like IBM and Google are already making breakthroughs. The problem? These machines can eventually break today’s encryption standards like RSA and ECC.
That’s where NIST-compliant Post-Quantum Cryptography (PQC) software comes in.
If you’re running a SaaS platform, cybersecurity business, or even a WordPress website handling sensitive data, this is something you can’t ignore anymore.
What is Post-Quantum Cryptography (PQC)?
Post-Quantum Cryptography refers to encryption methods designed to resist attacks from quantum computers.
Unlike traditional encryption:
- RSA depends on factoring large numbers
- ECC depends on discrete logarithms
Quantum computers can break both using algorithms like Shor’s Algorithm.
PQC uses new mathematical approaches such as:
- Lattice-based cryptography
- Hash-based signatures
- Code-based encryption
What is NIST-Compliant PQC Software?
To state it simply, Post-Quantum Cryptography consists of algorithms that are quantum-resistant in addition to being immune from any classical computer attacks.
The development of such algorithms and their implementation in software has been a worldwide race led by the National Institute of Standards and Technology (NIST). Late 2024 and 2025 marked the completion of the first group of standards (FIPS 203, 204, and 205), and software described as “NIST-compliant” utilizes such math problems that cannot be solved by a large-scale quantum computer.
What Does “NIST-Compliant” Mean?
The National Institute of Standards and Technology (NIST) has been working since 2016 to standardize quantum-resistant algorithms.
In 2025–2026, NIST officially selected key algorithms:
Approved PQC Algorithms:
- CRYSTALS-Kyber → Key encapsulation (encryption)
- CRYSTALS-Dilithium → Digital signatures
- SPHINCS+ → Hash-based signatures
- FALCON → Lightweight signatures
If software is NIST-compliant, it means:
✔ It follows these approved standards
✔ It’s safe for future quantum threats
✔ It’s trusted by governments and enterprises
Why US Businesses are Transitioning Now
The US government isn’t taking any chances. Under National Security Memorandum 10 (NSM-10), federal agencies and their contractors are already on a strict timeline to transition to PQC. But even if you aren’t a government contractor, here is why you need to pay attention:
- Harvest Now, Decrypt Later: Cybercriminals are currently stealing encrypted data and storing it. Why? Because they know that in a few years, a quantum computer will be able to unlock it. If your data isn’t protected by PQC software today, it’s already at risk.
- Regulatory Compliance: As NIST standards become the “gold standard,” industries like Finance and Healthcare in the US will likely see these integrated into HIPAA or PCI-DSS requirements.
- Future-Proofing: Updating your cryptographic infrastructure isn’t an overnight task. It requires an “Inventory and Assessment” phase that can take months.
The Big Three: Algorithms You Should Know
When looking for NIST-compliant Post-Quantum Cryptography software, you’ll likely see these names:
- ML-KEM (formerly Kyber): Used for general encryption, like securing websites.
- ML-DSA (formerly Dilithium): Used for digital signatures to verify identity.
- SLH-DSA (formerly SPHINCS+): A backup signature method based on different math to ensure total security.
How to Choose the Right PQC Software
Not all software labeled “Quantum-Resistant” is created equal. Here is a checklist for US-based decision-makers:
- Verified Compliance: Ensure the vendor explicitly mentions FIPS 203/204 compliance.
- Crypto-Agility: The software should be “agile,” meaning you can easily swap algorithms if a new vulnerability is discovered in the future without rebuilding your entire system.
- Performance Impact: PQC algorithms can be more “heavy” than traditional ones. Look for software that optimizes for speed and low latency.
- Hybrid Implementation: Many experts recommend a “Hybrid” approach—using both classical (RSA/ECC) and PQC layers simultaneously for maximum safety during this transition period.
Best NIST-Compliant Post-Quantum Cryptography Software (2026)
1. SandboxAQ AQtive Guard (Best for Discovery & Inventory)
Before you can encrypt, you must discover. SandboxAQ’s AQtive Guard is the industry leader for “Crypto-Agility.” It acts as an orchestrator that finds every vulnerable RSA or ECC key across your entire network and helps you swap them for NIST-standardized algorithms without breaking your production environment.
- USP: AI-driven automated inventory (CBOM generation).
2. QuSecure QuProtect (Best for Network-Level Security)
For businesses that need protection yesterday, QuSecure offers an “overlay” solution. It secures existing TLS and VPN connections using a hybrid approach—combining traditional encryption with NIST-compliant ML-KEM.
- USP: Real-time algorithm switching (Runtime Remediation).
3. IBM Quantum Safe (Best for Full-Stack Enterprise)
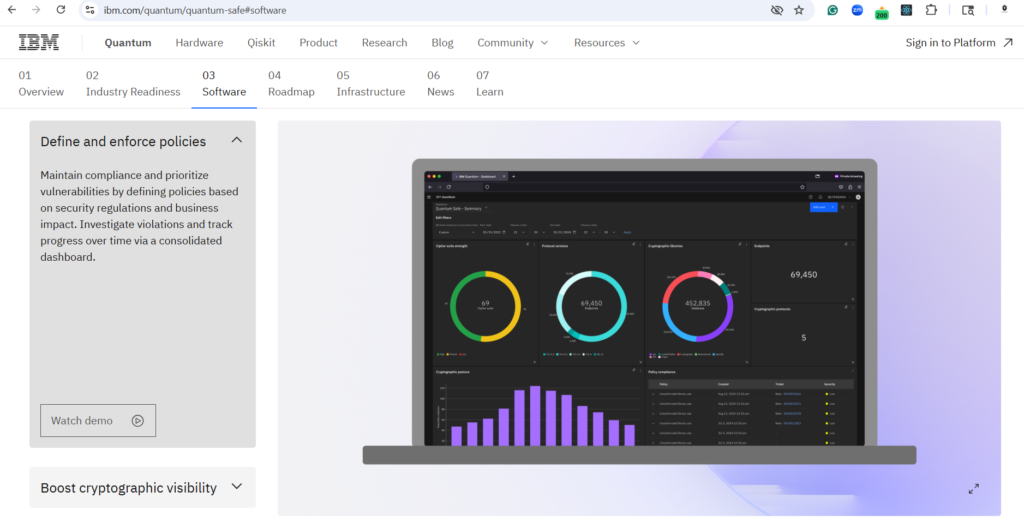
IBM has integrated PQC directly into its hardware and software ecosystems. From FlashSystem.ai storage to “quantum-resistant shells” for legacy apps, IBM provides a comprehensive roadmap for large-scale US enterprises.
- USP: Hardware-embedded PQC encryption.
4. AWS-LC & KMS (Best for Cloud-Native Organizations)
If your infrastructure is on Amazon Web Services, you’re already halfway there. AWS-LC is a FIPS-140-3 validated cryptographic library that was among the first to include ML-KEM. By using AWS Key Management Service (KMS), US businesses can easily generate and manage quantum-safe keys.
- USP: Seamless integration for cloud workloads.
5. PQShield (Best for SDKs and Embedded Systems)
For software developers building their own tools, PQShield provides highly optimized libraries and SDKs. Whether you are building a secure messaging app or IoT firmware, their NIST-compliant stacks are designed for high performance and low latency.
Comparison: Top PQC Solutions at a Glance
| Software Solution | Primary Use-Case | Best For |
| SandboxAQ | Discovery & Agility | Large Scale Inventories |
| QuSecure | VPN & TLS Overlay | Rapid Deployment |
| IBM Quantum Safe | Infrastructure | Full-Stack Modernization |
| AWS KMS | Cloud Management | Cloud-Native Apps |
| PQShield | SDKs & Libraries | Developers & OEMs |
How to Start Your PQC Migration (The 3-Step Plan)
- Inventory: Use tools like AQtive Guard or Qinsight to map your cryptography.
- Prioritize: Start with high-value data and internet-facing endpoints.
- Hybrid Deployment: Use a “Hybrid” model that runs classical and PQC algorithms simultaneously to ensure compatibility while you transition.
Final Thought
Quantum readiness is no longer a “tech trend”—it’s a compliance necessity. Is your organization ahead of the curve, or are you waiting for a breach to happen?








